The latest cryptographic technology that protects personal information on the cloud
—First, please explain encryption keys and decryption keys, both of which are essential elements of cryptographic technology.
Encryption keys and decryption keys are types of data respectively used to encrypt and decrypt digital data and play an important role in information security. They are used to protect and maintain data confidentiality by encrypting and “locking” data in the manner of a physical key so that only those with the correct key can decrypt those data. This process prevents misuse by third parties when personal information, such as account numbers and passwords, is being handled during online shopping or online banking. However, quantum technology is developing rapidly, and it is said that practical quantum computers will be available by 2030. When quantum computers arrive, information-processing capabilities will increase dramatically, and it has been found that conventional encryption methods, such as Rivest-Shamir-Adleman and elliptic curves, can be easily compromised. In response to this situation, new cryptographic technologies that can handle with the increased information-processing capabilities enabled by quantum technology are being researched and developed (Fig. 1).
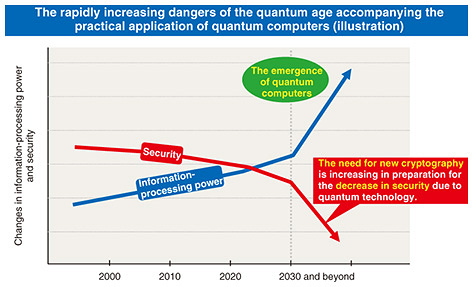
Fig. 1. Trends in information-processing capabilities and security of computers.
Let us start with an example of the capability of current cryptographic technology. Instead of traditional one-to-one communication, one-to-many or many-to-many communication, as seen in cloud environments, is becoming increasingly common. Online meetings involving multiple participants are a good example of this communication. In such one-to-many or many-to-many communication, it may not be possible to provide the same information to each participant, and standard encryption designed for one-to-one communication may be insufficient. For example, let us assume an important internal company meeting, including discussion of company secrets, is held online with participants ranging from executives to general employees, each of whom has different positions and roles. By distributing the same encrypted meeting materials to all participants and providing them with different decryption keys according to their roles, it is possible to control information disclosure precisely. Specifically, by assigning a key that can decrypt all content to managers at the department-head level and above and a “restricted” key that prevents the decryption of confidential information to other employees, it becomes possible to hide information that must be kept secret (Fig. 2).
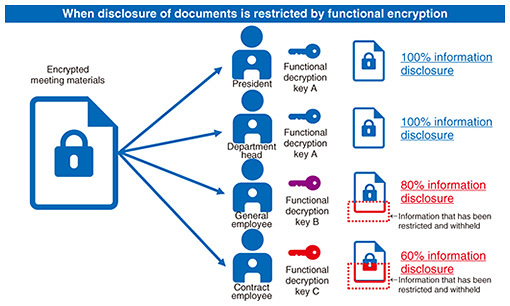
Fig. 2. Examples of functional encryption.
This type of encryption, which allows for precise control over the information obtained from a single data point via the decryption key held by each participant, is called “functional encryption” and is suitable for one-to-many and many-to-many communication. Regarding computers and smartphones used today, most personal information, including photos, is stored in the cloud. The need to apply security measures to this cloud-stored information and data is now urgent.
—Would you explain data security in the cloud?
When subscribing to an application or service, users are given a long string of characters, such as an ID (identifier) and password, and granted permission to use the service by entering that string and being authenticated. However, if a user is already using cloud storage (external storage), such complex authentication information is probably stored in the cloud and used in an automated form. However, the risk that data stored in such external storage may be misused is always present. For example, credit-card numbers stored in the cloud for use in online shopping may be hacked. Even if the user presumes that the credit-card information was deleted after the contract period of the credit card expired, it is still possible that a copy of the information exists somewhere in the cloud.
It is impossible to delete data and information completely with traditional (classical) computers. Even in the case of “deleted data,” which might be stored in the cloud as mentioned earlier, companies regularly back up all their data, so if something goes wrong with the entire system and the backup data (data existing before the deletion) are replaced without notice, there is a non-zero possibility that the supposedly deleted data could be recovered. With current classical computers, it is possible to make countless copies of digital information, so proving that no copies remain anywhere is providing the so called “devil’s proof.”
However, the use of quantum information technology for computing completely changes this situation. Under the assumption of the existence of a quantum computer, by exploiting the properties of quantum mechanics, it becomes possible to generate—in quantum states—ciphertext and private keys (decryption keys) that can provide complete “proof of deletion” (Fig. 3).
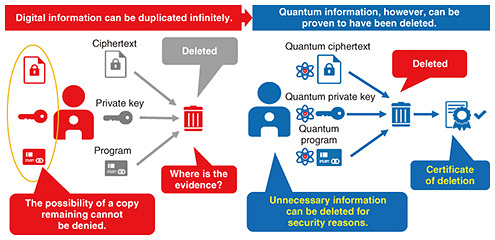
Fig. 3. Proof of deletion enabled by combining quantum information technology and cryptography.
As the practical application of quantum computers gradually approaches, cryptographic technologies that can only be implemented by utilizing the capabilities of quantum computers are expected to become essential.
—Would you explain “proof of deletion” using quantum information technology in more detail?
Basically, most cryptographic technologies can be broken if the computing power used to break them is extremely high. Current cryptographic technologies are valid based on the idea that calculations to break them using classical computers are extremely difficult and time-consuming. However, if the original ciphertext can be completely deleted, even if a computer with infinite computing power is developed in the future, the content of the ciphertext will remain completely unknown after it has been deleted.
Using approaches such as “proof of deletion” and “secure sharing of information,” I’m researching cryptographic technologies for the quantum-computing era. As I mentioned above, however, so long as classical computers are in use, it is impossible to prove that information has been deleted or that information (such as decryption keys) has been returned. However, technologies that apply the uncertainty principle of quantum mechanics can use the property that when a certain amount of information is observed, it becomes impossible to observe its counterpart simultaneously with sufficient precision. Applying this property makes it possible to generate a ciphertext of a quantum state then erase that ciphertext, and evidence of that process provides a “certificate of deletion” proving the data have been securely deleted. If this certificate is validated, it can be guaranteed that no information about the original message can be obtained. If a decryption key for the quantum state is generated and lent to information users, the users can send back a certificate of deletion of the key upon return of the key to prove that it was deleted. Under the assumption of the existence of such quantum computers, my research is proceeding from the perspective that we can implement cryptographic functions enabled for the first time (Fig. 4).
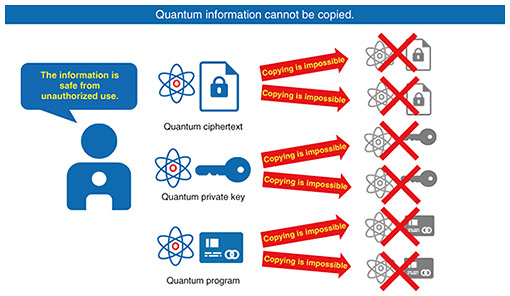
Fig. 4. Impossibility of copying due to the nature of quantum mechanics.
—Would you tell us about any difficulties you encountered during your research and any challenges that you anticipate need to be addressed in your future research?
The field of cryptography has seen a rapid increase in the publication of various research papers. In fact, I have published numerous research papers and presented them at top cryptography conferences such as Symposium on Theory of Computing (STOC), Crypto, and Eurocrypt. The many papers that I’ve had accepted include eight on public-key cryptography presented at Crypto, nine on quantum cryptography presented at Eurocrypt, two on program watermarking presented at STOC, and eight on program obfuscation published in the Journal of Cryptology (a prestigious journal on cryptography). I’ve also applied for many patents. Initially, I was a little bewildered in trying to keep up with the pace of and adapting to this cutting-edge research. Back then, I needed time to change my mindset when my research was not progressing as I hoped. However, I have overcome these challenges by finding ways to change my mindset, such as exercising (namely, swimming), which I have been doing since my student days.
From a technical standpoint, my research is purely theoretical, and even for post-quantum secure cryptography compatible with quantum computers, which are expected to be put into practical use by 2030, no actual machines are currently available for practical testing. While I know that my proof of deletion technology is theoretically possible, the future challenge will be how to modify it to make it a more-complete technology and put it into practical use once practical testing becomes possible.
To contribute to innovation in all information-related industries
—Would you tell us what this research will achieve and what its future applications might be?
I anticipate the post-quantum secure cryptography and proof of deletion technologies that I’ve developed will be used for subscription services including video streaming, music streaming, software distribution, and public services. Most subscription services operated by various companies currently control user usage through their own systems. For example, if paid-for videos were encrypted and the user was given a private key (decryption key) to enable them to view the video, illegal downloads and illegal data distribution would decrease and result in safer viewing for users. Even if the contract period expires, the streaming company’s profits would likely be guaranteed through the return of the private key or proof of its deletion.
By applying proof of deletion, it may become possible to lend programs (apps) securely. For example, if users could try out an app and return it after the trial period, proof of deletion would guarantee that no app information remains on the user devices and, in turn, reduce the possibility of pirated versions of the app circulating. It could allow for flexible app distribution while protecting the interests of the app provider. If the potential of proof of deletion is fulfilled, it could not only protect copyrights but also contribute to security of all content industries worldwide.
With the introduction of NTT’s IOWN (Innovative Optical and Wireless Network), cryptographic technology will be indispensable wherever information is exchanged, not only in the ever-expanding world of communications but also in fields such as software development and application and game development. It will continue to evolve and change in form in line with the development of network environments. I intend to continue researching and developing new, impactful cryptographic technologies that are compatible with these evolving network environments.
—Would you give us your thoughts on research and what you value most?
I’ve been researching cryptography, from my university years and after joining NTT, for nearly 20 years. I follow two criteria for choosing research topics. The first is it must be something that excites me, that is, I must feel in my heart that “this is absolutely fascinating.” The second is it must be a technology that I believe will be “useful” in the future. In addition to those criteria, if I have choices and I’m unsure of which one to make, I choose the more difficult, challenging one. I share and practice this approach within my research group.
—Would you describe your impression of NTT Social Informatics Laboratories, where you work?
In short, NTT Social Informatics Laboratories is a research institute that primarily conducts research on security. Its research on security covers a wide range of topics from a diverse range of perspectives. In addition to researchers specializing in system-based security, such as network security and operating-system security, some departments conduct research on security from the perspective of human safety and sense of security, and other departments deal with security related to the rights of voices, such as those of regular actors and voice actors, from a legal perspective. Our researchers thus have diverse backgrounds with expertise not only in communications but also in law, psychology, and other fields.
NTT Social Informatics Laboratories offers a flexible work environment. While work is primarily remote, my research group comes into the office once a week for meetings and discussions. I believe that casual conversations related to research are also important, so this once-a-week office visit enables everyone to meet face-to-face and chat. In fact, new ideas and research topics have been discovered through these chats, and clues to solving problems we are facing have been found, so it is a very effective initiative.
—What is your message for our readers, researchers, students, and business partners?
NTT’s research on cryptography ranks as one of the best in the world. We thus receive applications from overseas for internships in my research group every year, and many international students stay with us for certain periods. It is also not uncommon for leading researchers from overseas to visit us as guest speakers. These guests are always invited to give lectures that are open to all. Since I’m a visiting professor at Institute of Science Tokyo (formerly Tokyo Institute of Technology), I give lectures to students a few times a year. I also try to reach out to the students I meet at these lectures as well as research labs at various universities, and I invite them to the lectures presented by our guest overseas researchers. In fact, most of the researchers currently in my research group are people I met through these interactions. Without doubt, students and researchers who want to broaden their horizons by communicating directly with renowned overseas researchers and conduct research with a global impact should come to NTT. Our lectures by overseas researchers are open to everyone, and I hope you will take the chance to attend. Finally, I’d like to express my sincere hope that we can continue to advance our research in a positive relationship with our business partners who have been cooperating with us. Thank you for your continued support.
